Lexitrace
Theme:
Value
“In 2022, the average cost of a data breach has reached a record high of US$4.35 million, according to the 2022 cost of a data breach report by IBM and the Ponemon institute.” (Source)
For a small cost, we will integrate our solution with your system, so that you can identify and deter future breaches in your system.
Use Cases
| |
| |
| |
|
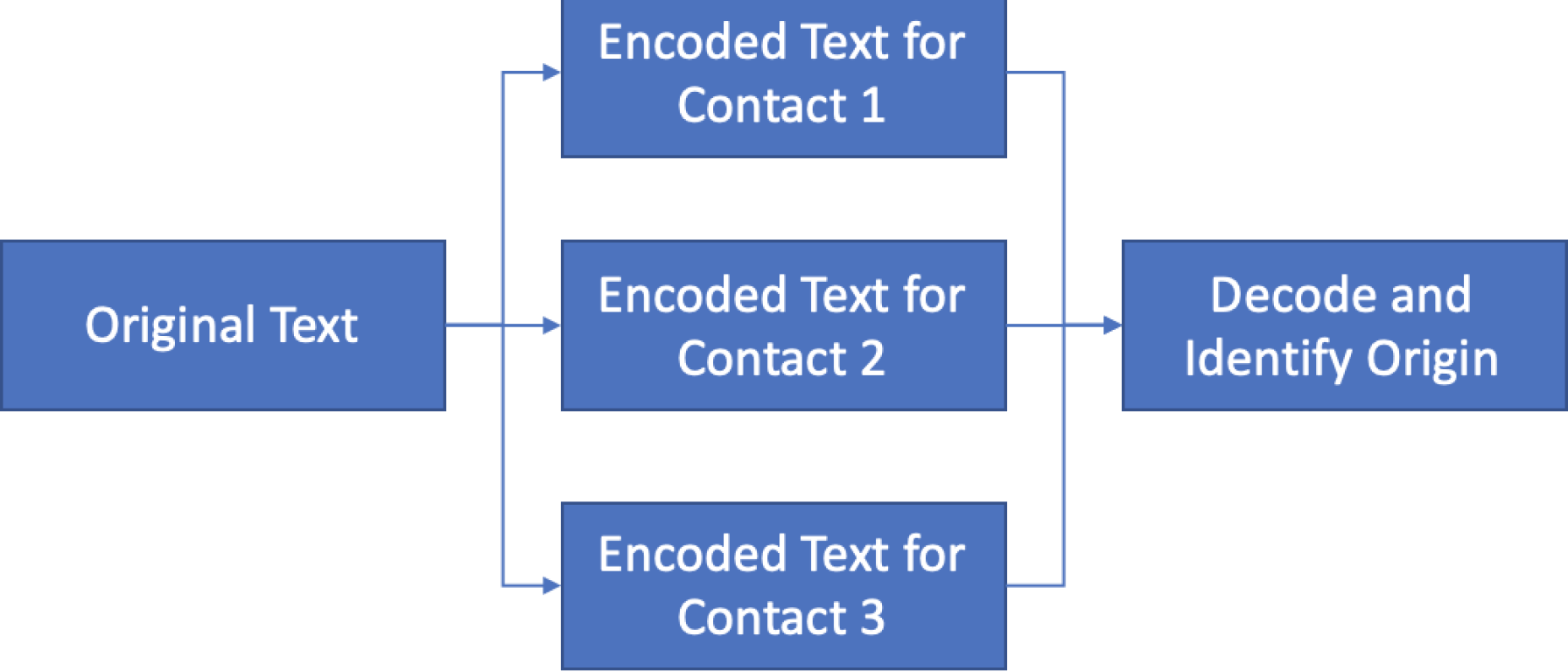
Method
| |
| |
| |
 | |
Contact
If you are interested in integrating our application with yours by API, please contact us here, and we can provide pricing.